OneLogin
OneLogin Integration¶
Comet supports OAuth2 authentication from an approved OneLogin application. Once an OneLogin application has been integrated, a specific Comet URL can be used to login.
New users logging in for the first time will automatically have a new user created using onelogin user information. Once logged in the user can perform all actions a normal login provides.
Basic Requirements¶
Prerequisites Comet Implements an OAuth 2 OpenID Connect Authorization Code Flow through OneLogin. The OneLogin Documentation to setup an Application can be found here.
A sample application has been highlighted below.
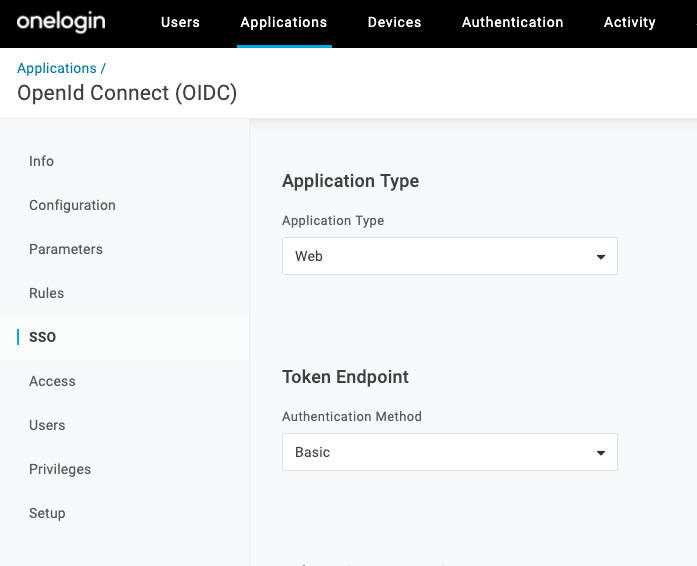
Once the Onelogin application is successfully created, go to the Application SSO tab.
Application Settings¶
On this tab, there are two configurable parameters to set. The Application Type should be set to Web, and the Token Endpoint Authentication Method should be set to Basic
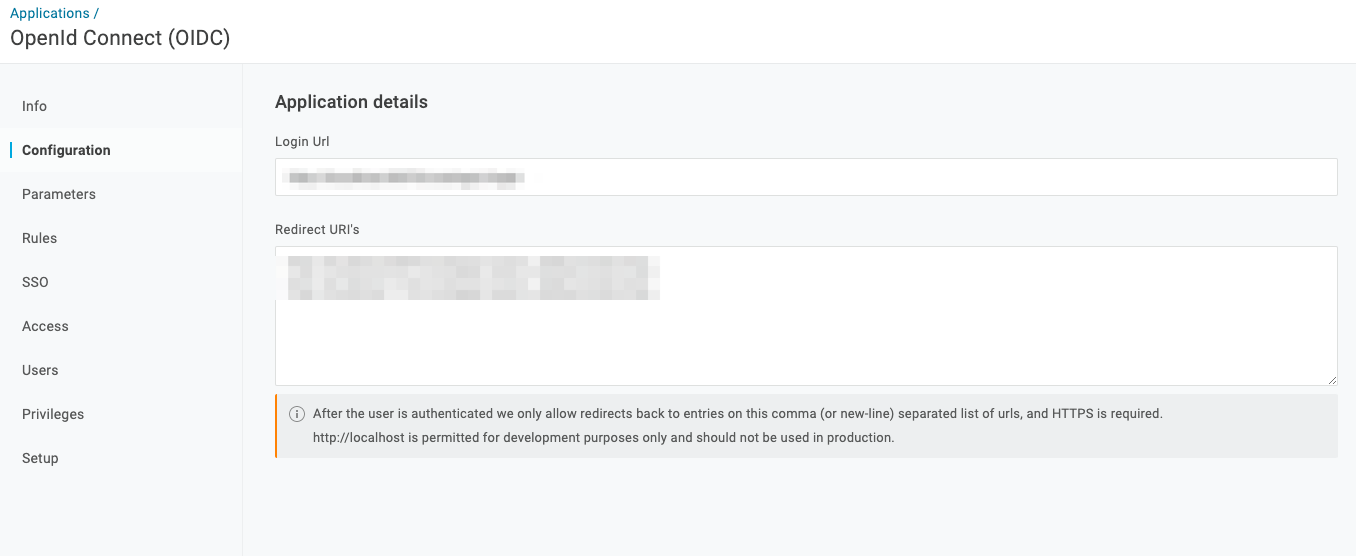
Once these have been set, head on over to the Application Configuration tab.
This tab contains another two configurable parameters to set. The Login URI starts the auth process and must be set to https://company-comet-domain/onelogin-login The Redirect URIs are used to complete the auth process and must be set as follows:
https://company-comet-domain/api/onelogin/oauth_callback/onelogin
https://company-comet-domain/api/auth/logout
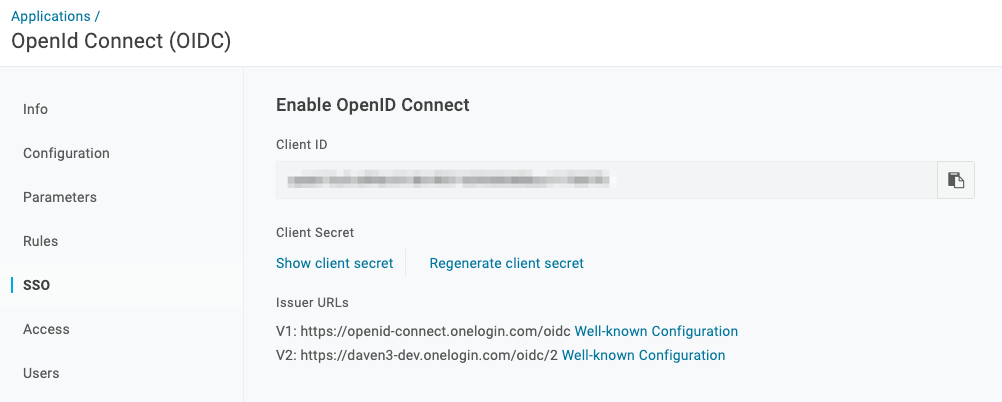
Redirect URIs are callback endpoints that OneLogin uses to send authentication responses and ID tokens. The Logout URI is the location OneLogin will redirect the user after logout by OIDC. If you do not want to redirect after logout you can leave this blank Applications - SSO This tab contains the ClientID and Client Secret which are used to authenticate the Onelogin Application to Comet.
Take note of the credentials as you'll be using these shortly.
Configuring Comet to use Onelogin on Linux installs¶
Run cometctl aio update-config and set/replace the following variables:
Replace the existing environment_token with the following value: environment_token: onprem-onelogin-auth
Append the following to the end of the file, replacing on_prem_one_login_client_key and on_prem_one_login_client secret with the credentials retrieved from the previous step.
one_login_oauth_enabled: true
on_prem_one_login_client_key: "ClientID"
on_prem_one_login_client_secret: "ClientSecret"
If you're configuring this as part of your installation, you may now run cometctl aio install
Configuring Comet to use Okta on Kubernetes/Helm installs¶
Set the following variables in your local values.yaml.
frontend:
environmentToken: "onprem-okta-auth"
backend:
oneLoginOauthEnabled: true
oneLoginClientKey: "ClientID"
oneLoginClientSecret: "ClientSecret"
helm upgrade --namespace default -f values.yaml comet-release comet-ml/cometml